



“The demo blew us out of the water.”
“Being able to tell what's in use is phenomenal.”
“This is one of those tools you can pry from my cold dead fingers.”
“It's very great. It's awesome.”
“It's just a Swiss army knife of utility for us.”
“You've just transformed a six-hour project into an hour of work.”
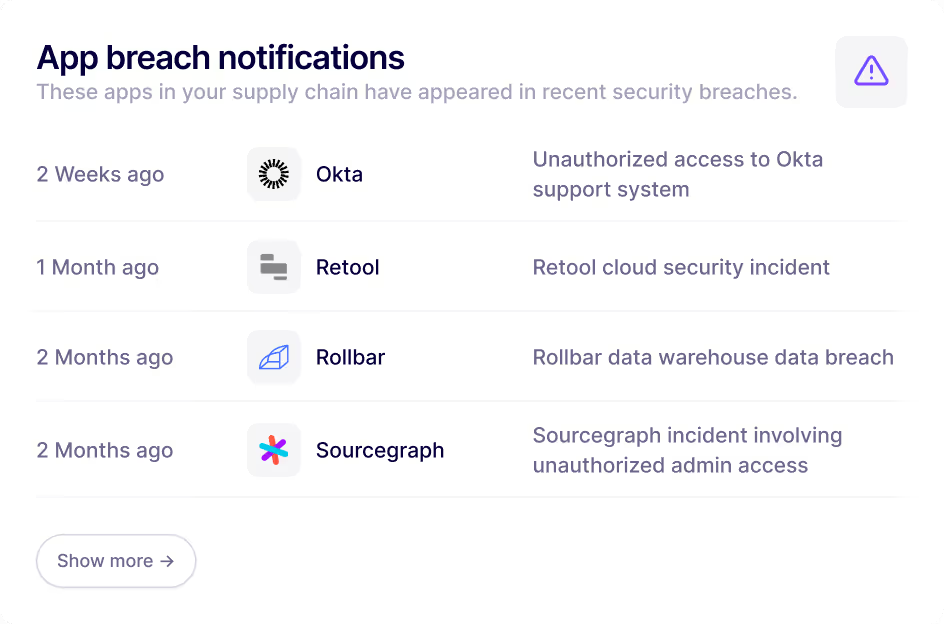
“The visibility into software supply chain breaches blew me away.”
“I really, really like this app.”
“The demo blew us out of the water.”
“Being able to tell what's in use is phenomenal.”
“This is one of those tools you can pry from my cold dead fingers.”
“It's very great. It's awesome.”
“It's just a Swiss army knife of utility for us.”
“You've just transformed a six-hour project into an hour of work.”
“The visibility into software supply chain breaches blew me away.”
“I really, really like this app.”
A complete shadow IT inventory—delivered in minutes, maintained automatically.









From zero visibility to a full shadow IT inventory in hours, not days.
Why modern security teams ❤️ Nudge Security
Common questions about Nudge Security's shadow IT solution
Shadow IT refers to the use of technology systems, devices, software, applications, or services without the explicit knowledge or approval of an organization’s IT department. This often happens when employees adopt third-party tools—especially cloud-based or SaaS applications—to improve productivity, bypassing formal approval processes. While shadow IT can accelerate workflows, it introduces risks because these tools may not comply with security policies, data governance standards, or licensing agreements.
While shadow IT can support innovation and productivity, it introduces significant risks. Unapproved applications may expose sensitive data, create regulatory compliance gaps, or increase the likelihood of data breaches. Shadow IT also leads to duplication of tools, inconsistent workflows, and unmonitored spending. Organizations without visibility into shadow IT often struggle to enforce security policies, manage budgets, and maintain operational consistency across departments.
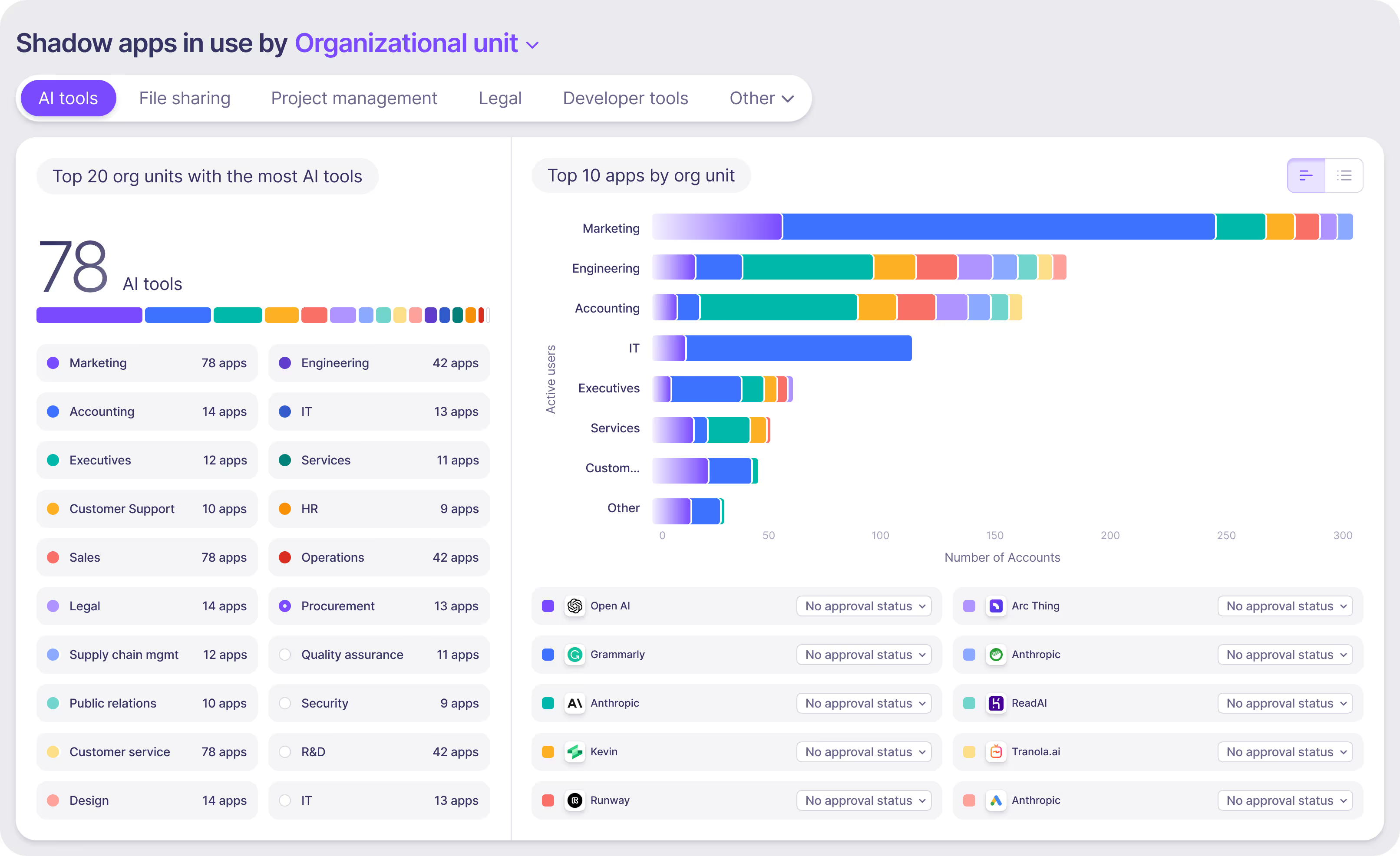
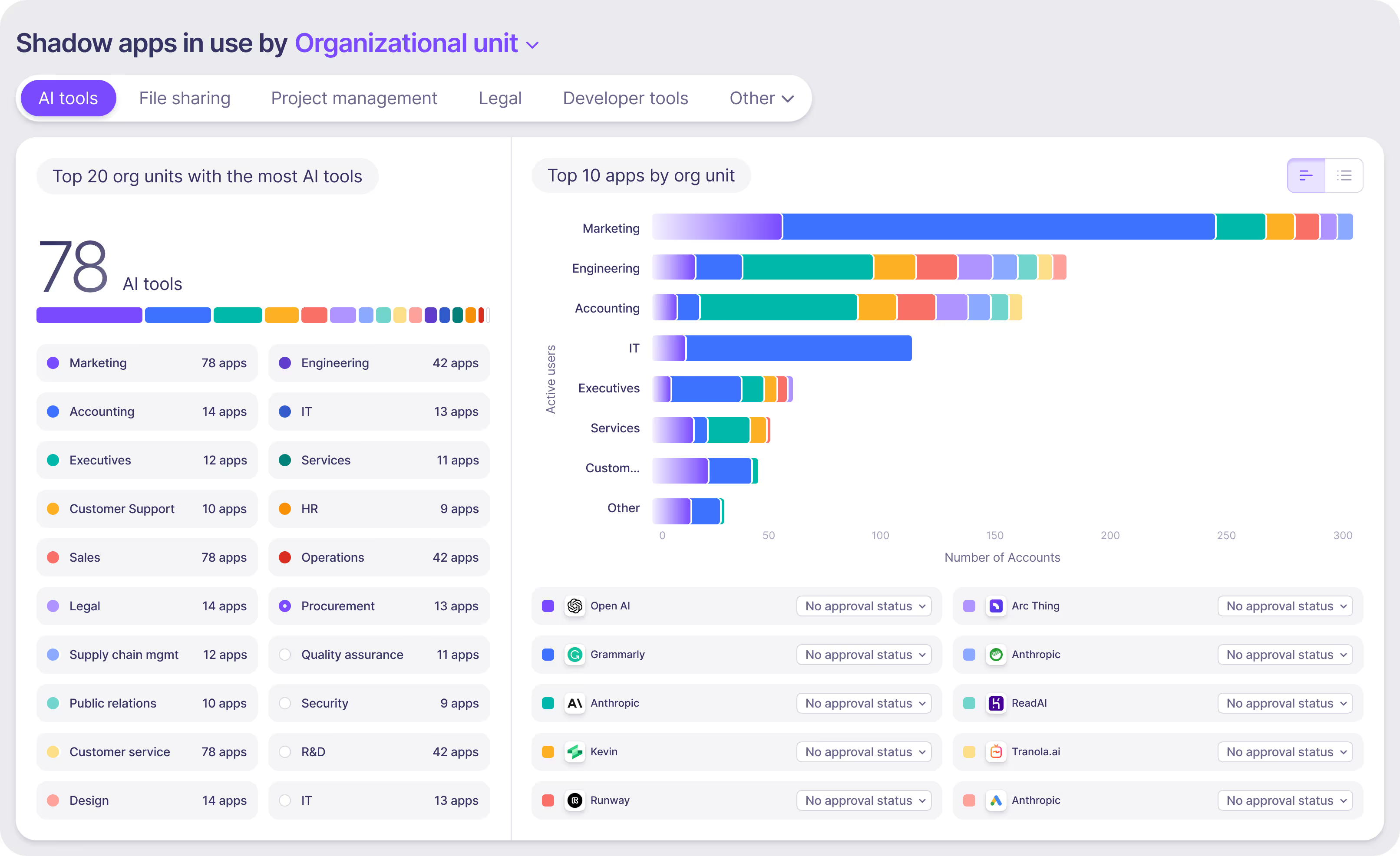
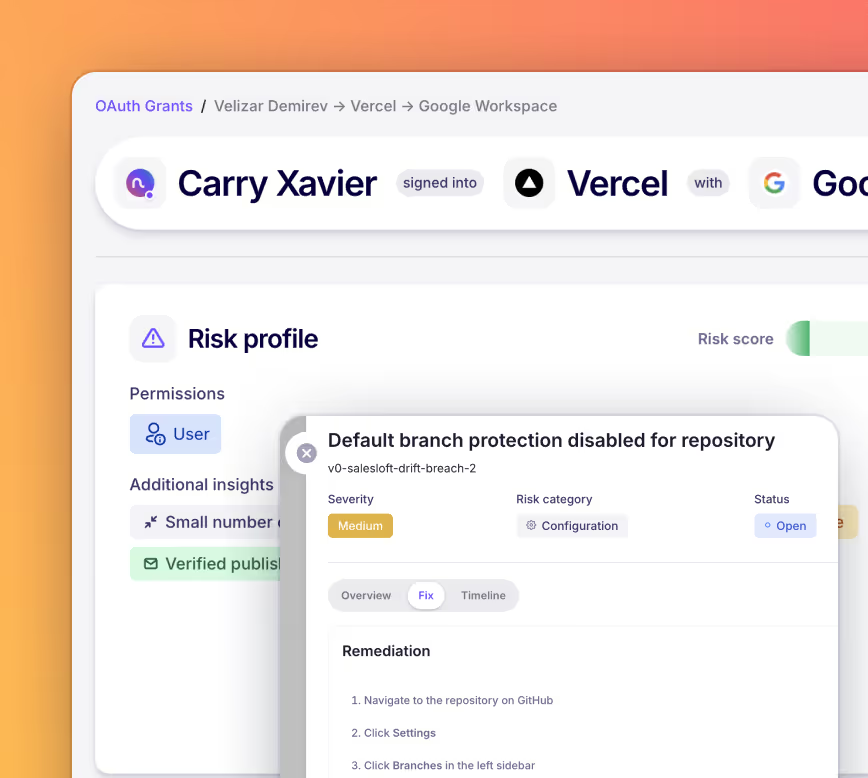
Nudge Security provides a unified, comprehensive inventory of all SaaS and cloud applications in use across an organization. It detects apps, accounts, and integrations introduced outside IT oversight, including both approved and unapproved tools. By combining billing, identity, and usage data, Nudge surfaces hidden or unauthorized applications, enabling teams to understand where shadow IT exists and how it impacts both security and spend.
Nudge Security identifies multiple forms of shadow IT, including:
• SaaS and cloud applications adopted outside of IT oversight
• User accounts and identities created without approval
• Third-party integrations and services that may pose security or compliance risks
This visibility helps organizations regain control over their technology environment, reduce risk, and consolidate or retire unnecessary tools.
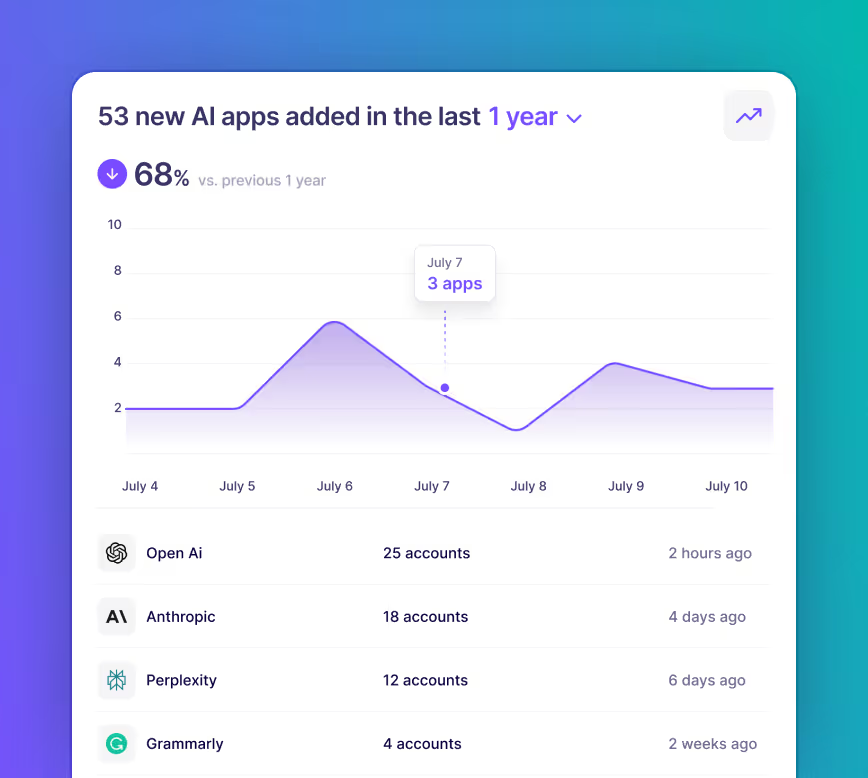
Nudge Security is designed for rapid deployment and fast time-to-value. Within minutes of activation, your SaaS inventory begins to populate automatically. Historical billing and usage data can be ingested immediately, giving insights into adoption patterns, unapproved tools, and spend anomalies even before a full discovery cycle completes. Many organizations identify potential savings or risky applications within days of deployment.
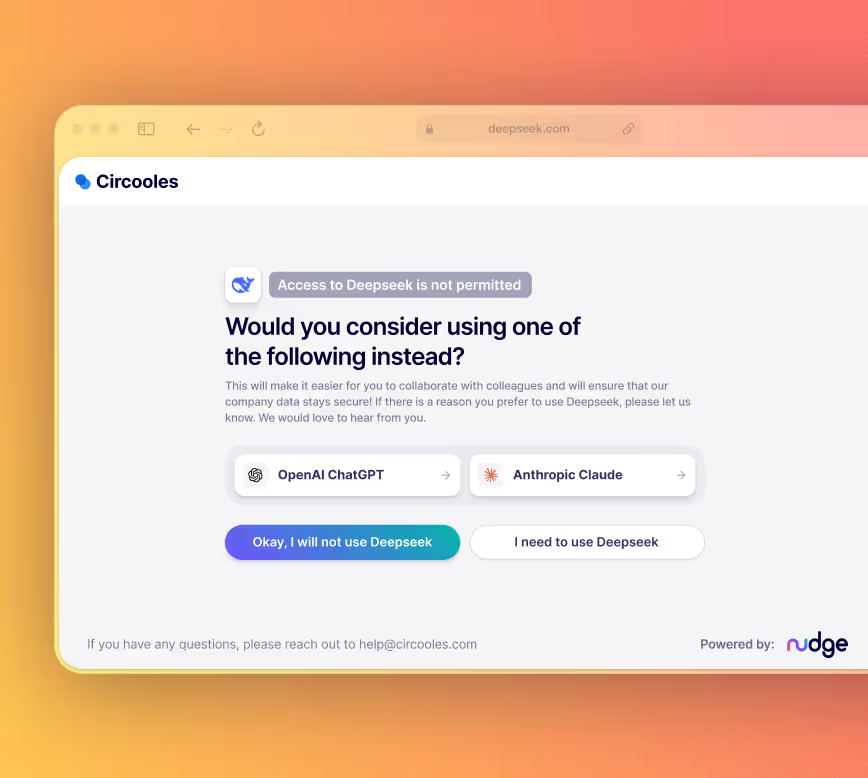
No. Nudge Security does not prevent employees from using shadow IT. Instead, it provides visibility and actionable insights so organizations can guide employees toward approved tools, educate them on security risks, and enforce governance policies. This approach balances security and productivity, allowing teams to make informed decisions without interrupting workflows.
Nudge Security is built with privacy and security at its core. It typically requires read-only access to accounts, analyzes data in memory, and only stores metadata necessary for reporting and governance. Sensitive content, such as emails or documents, is not retained, and every action is auditable. This ensures organizations can gain visibility into shadow IT while maintaining compliance with internal privacy policies and external regulations. To learn more about how we limit and safeguard our access to your email account, visit our Trust & Security page.
Unlike traditional network or endpoint security tools, Nudge Security takes a SaaS-first approach. It focuses on discovering and managing cloud applications and AI tools, including those adopted outside IT’s control. This provides a comprehensive view of both sanctioned and unsanctioned applications, enabling organizations to manage risk, enforce governance, and optimize spend across the entire SaaS landscape—something network-centric tools alone cannot achieve.
Yes. By providing visibility into all SaaS applications in use, Nudge Security helps organizations assess compliance with internal security policies and regulatory standards. Teams can prioritize review of high-risk applications, ensure proper provisioning and deprovisioning of accounts, and maintain a documented inventory of all cloud tools. This makes it easier to demonstrate compliance during audits and reduces exposure to regulatory penalties.
Getting started is straightforward. Organizations can sign up for a trial to begin discovering all SaaS apps in use across the environment. Deployment is fast, requiring minimal configuration, and Nudge begins producing insights immediately. From there, teams can automate governance workflows, remediate risky applications, and integrate shadow IT oversight into existing IT and security processes. This allows organizations to secure their technology landscape without disrupting ongoing productivity.