


SSO tax be damned. Every Nudge Security customer can take advantage of SSO functionality to enable sign in with Okta at no extra cost.
Vary the access needed by role, including granting every employee the ability to self-manage their SaaS footprints.
Extend Nudge data to the rest of your IT security stack including SecOps, ITSM, identity management, and more.


Curbing shadow IT is a manual, disruptive, and delayed forensics process (if done at all).

Employees are frustrated by archaic IT policies. They find workarounds or worse—new jobs.

Spreadsheets are used to track compliance scope, access reviews, SSO enrollment, and more.

Third-party vendor risk assessments are conducted infrequently with stale vendor data.

Employees retain access or leave orphaned accounts when exiting or changing roles.

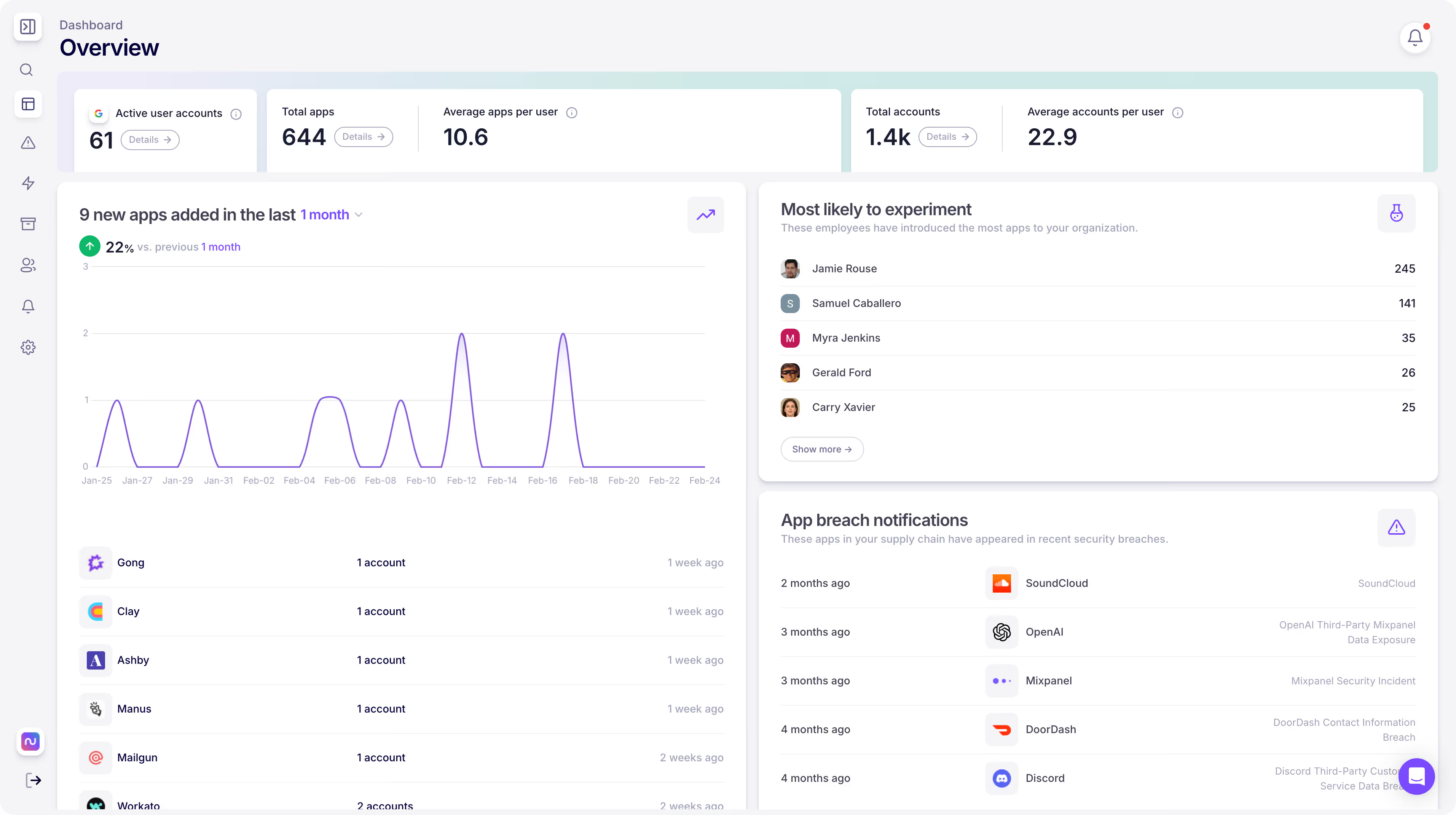
SaaS assets are discovered and categorized as soon as they are created, anywhere, any device.
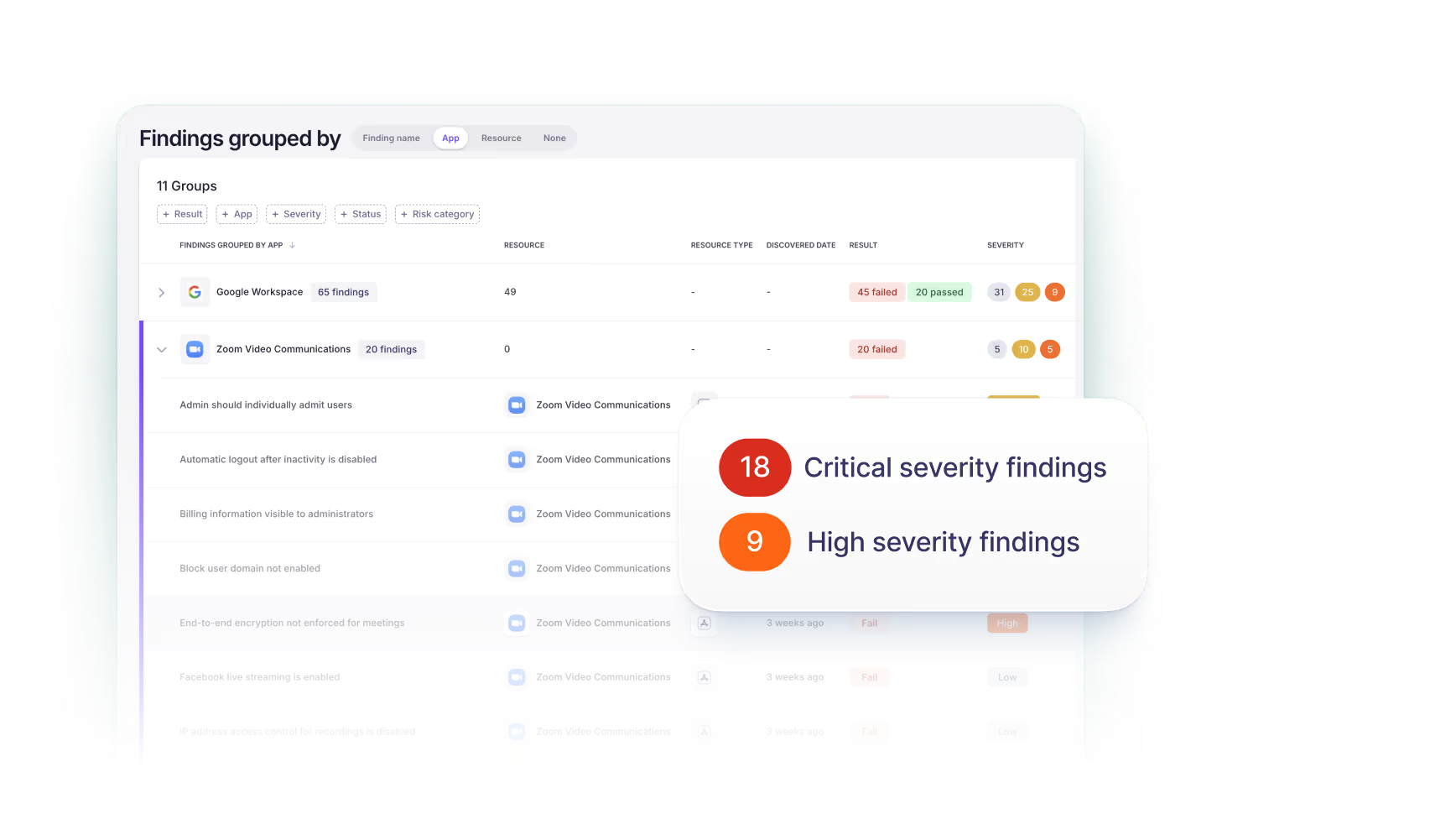
Risks and misconfigurations are continually surfaced, prioritized, and assigned to the right people for fast resolution.
SaaS vendor risk, supply chain, and breach data is gathered continuously and independently.
Empower your workforce to use new SaaS and GenAI technologies without losing oversight or adding overhead.
Employee offboarding is streamlined and secure, with automated workflows to transition accounts and owned resources.
Listen, we didn’t set out to build another security technology that sits between your employees and their work. Besides, tools that block access to SaaS applications didn’t solve shadow IT problems, they just pushed SaaS usage deeper into the shadows.
Nudge Security does not block or limit access to SaaS applications. Instead, we make it easy and automated for you to reach out to employees as soon as they start playing around with new SaaS tools, so you can guide them towards sound security decisions, whether that’s to enable security settings, use an alternative application, or even delete the account. As research shows, security nudges lead to better security outcomes than blockades.
Other companies focused on SaaS security management include Wing Security, Grip Security, Valence Security, Push Security, and Lumos. Nudge Security's patented discovery method allow us to find the shadow IT other providers can't, and its AI-powered SaaS vendor security profiles enrich that data with actionable insights. And unlike the alternatives, Nudge Security believes that every employee has the potential to support an organization's cybersecurity posture. Nudge Security's approach is founded on the belief that the best way to scale SaaS security and governance is to harness the power of the modern workforce.
Unlike a CASB or SASE solution, Nudge Security does not touch the corporate network or endpoints. It does not require your employees to be on a VPN or corporate network to work, nor does it require you to do an enterprise roll-out of an agent. It just works no matter what device the employee is using or where they are using it from.
Nudge Security takes a different approach to SaaS security—one that puts employees at the center of their own SaaS adoption and use. We use a lightweight, non-disruptive method to detect new SaaS accounts and help IT security teams to automate outreach to employees, nudging them to use an alternative application, enable MFA, or provide additional context about their SaaS use. Read more on our comparison page.
Most SaaS security and SaaS management platforms require that you already know which applications are in use in your organization. Nudge Security's SMP starts with SaaS discovery, so you can work to secure your entire SaaS estate, not just the vendors that procurement knows about. Some solutions do provide some pseudo-discovery capabilities, often relying on expense reports (hello? freemium apps?) or integration with a CASB or network monitoring tool. If you already have an SSPM or SPM solution that you like, Nudge Security is a great complementary service.
The other main delta is that traditional SSPM and SPM tools often work solely by connecting directly with the SaaS applications they govern and often boast the number of integrations they support: 5, 20, a whopping 20. Yet, there are some 20,000 SaaS companies on the market today and rising. It’s a sisyphean approach to solving the SaaS security problem. Nudge Security's SMP takes a different approach, one that enables you to secure the long tail of SaaS applications by engaging employees in basic security hygiene tasks like enabling MFA and providing your team with rich security context. Building on that approach, Nudge Security also integrates with critical apps for even deeper insights, security posture checks, and automations.
Read more about Nudge v. SSPM and Nudge v. SMP on our comparison pages.
