We surveyed 375 IT professionals to better understand the current state of employee offboarding.
From last year’s Great Resignation to this year’s headlining layoffs, if there’s one word to describe the labor market as of late, it’s “volatile.” Amidst all of this volatility, IT organizations are under immense pressure to maintain normal business operations and to protect corporate assets as employees come and go. It’s no small feat. In today’s highly distributed, cloud-first organizations, simply knowing where all corporate data resides and who has access to it—an essential prerequisite to employee offboarding—proves to be a big challenge.
We recently surveyed 375 IT professionals to better understand the current state of employee offboarding. Specifically, we wanted to better understand how IT organizations clean up an employee’s cloud and SaaS footprint whenever they change roles or exit the organization. (Learn more about how you can automate SaaS offboarding with our new playbook.)
The results tell a curious story. Respondents felt overwhelmingly confident about their IT offboarding processes—but should they?
Despite their confidence, respondents reported spending hours of manual effort, sifting through multiple disparate sources of information, and coordinating across multiple departments to offboard cloud and SaaS access. And yet, things still get overlooked. The majority of respondents have experienced business disruption, security incidents, and/or wasted spending as a result of ineffective offboarding.
Our survey results point to a looming question: “Have IT organizations resigned themselves to the status quo of a tedious, time-consuming, and incomplete offboarding process?”
79% of respondents feel confident in their IT offboarding process. Yet, at the same time:
To put that into perspective, Meta’s 2023 layoffs alone would take a single, full-time IT administrator 26 years to finish offboarding. Absurd, I know. While you can assume that large enterprises employ some IT automation to offboard at scale (and more than one IT administrator), our survey results show that current levels of investments in IT automation didn’t significantly affect how much time respondents spend on offboarding activities.
As it turns out, deprovisioning an employee’s access to cloud and SaaS applications isn’t as simple as flipping a switch in the corporate identity provider (IdP) or single sign-on (SSO) system. Much of the work is still manual, tedious, and time-consuming. As such, IT organizations are spending hours compiling a list of an employee’s cloud and SaaS access, deleting and transferring data, and coordinating with application business owners to reclaim or reallocate unused SaaS licenses.
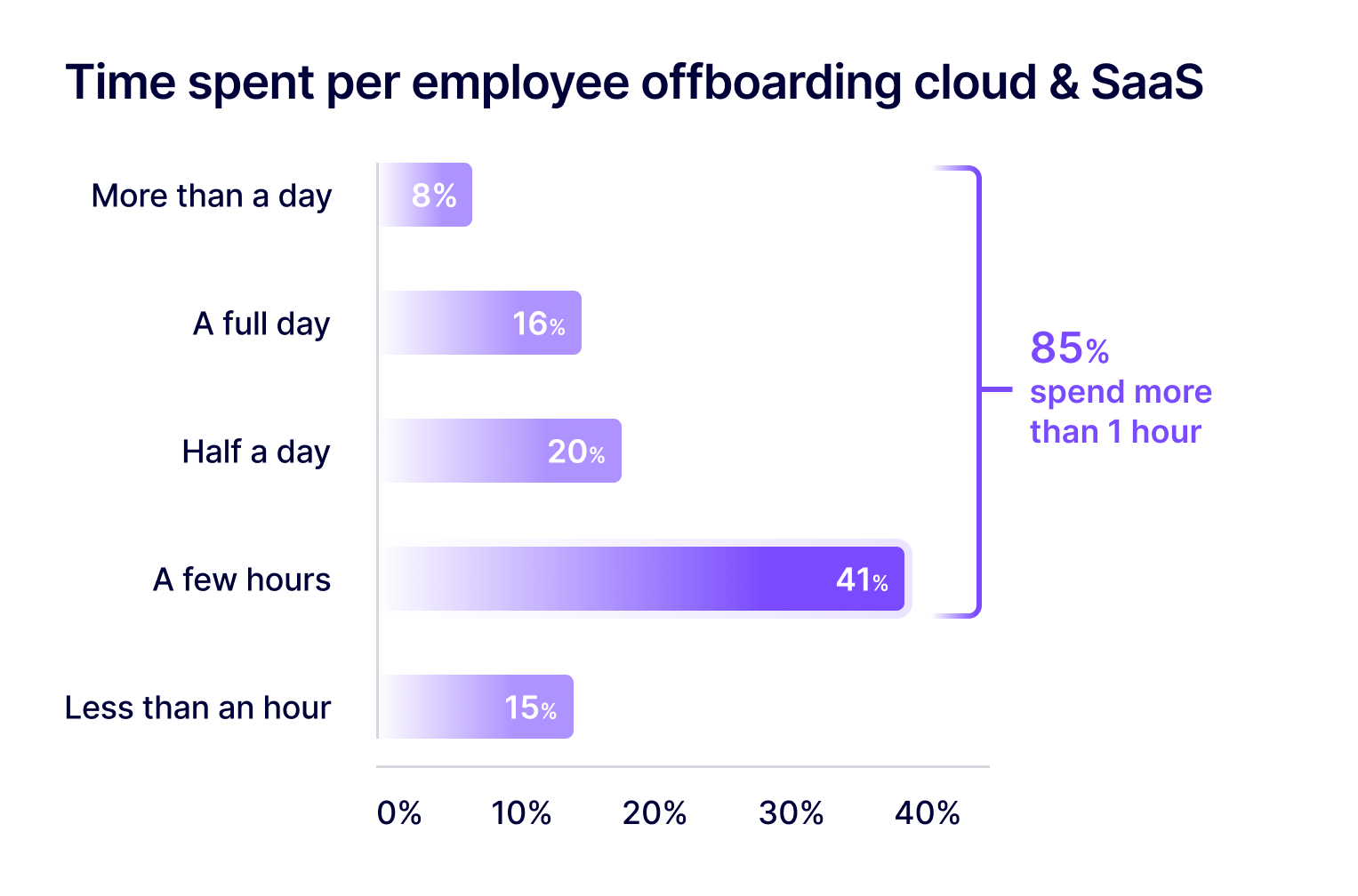
We asked this question in two different ways in our survey, and the results of each question matched up well. First, we asked, “How much time do you spend identifying and deprovisioning all cloud and SaaS accounts the employee had access to?” 85% reported spending a few hours or more.
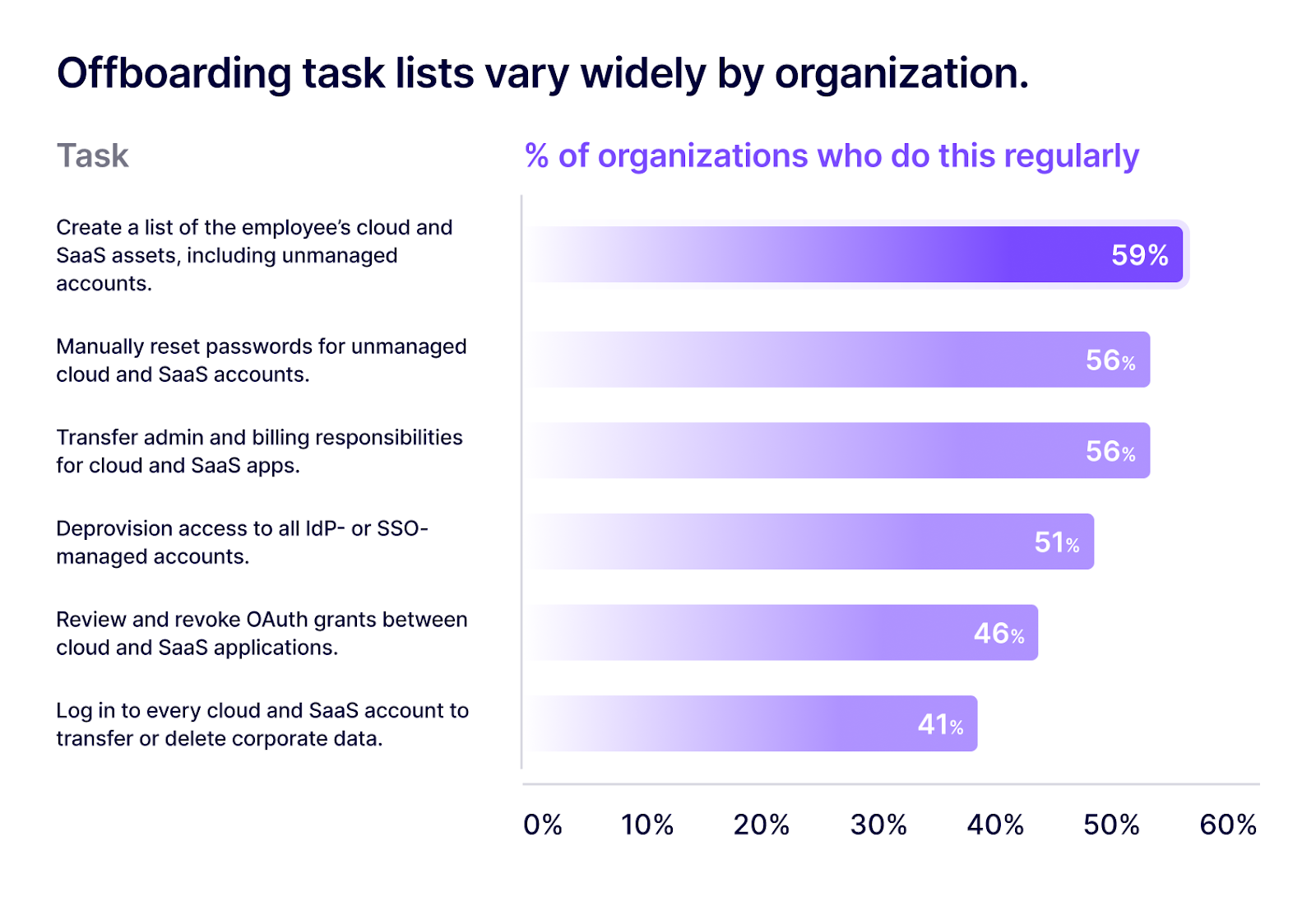
We then asked, “Which of the following activities do you (or another person in your organization) perform regularly as part of your IT offboarding process?” 64% of overall respondents regularly perform 3 or more of the following activities:
For each activity a respondent selected, we asked a follow-up question, “On average, how many minutes do you spend on [this activity] when an employee leaves your organization?” We tallied these averages and removed outliers to reach a conservative estimate of 5 hours per employee spent on cloud and SaaS offboarding tasks.
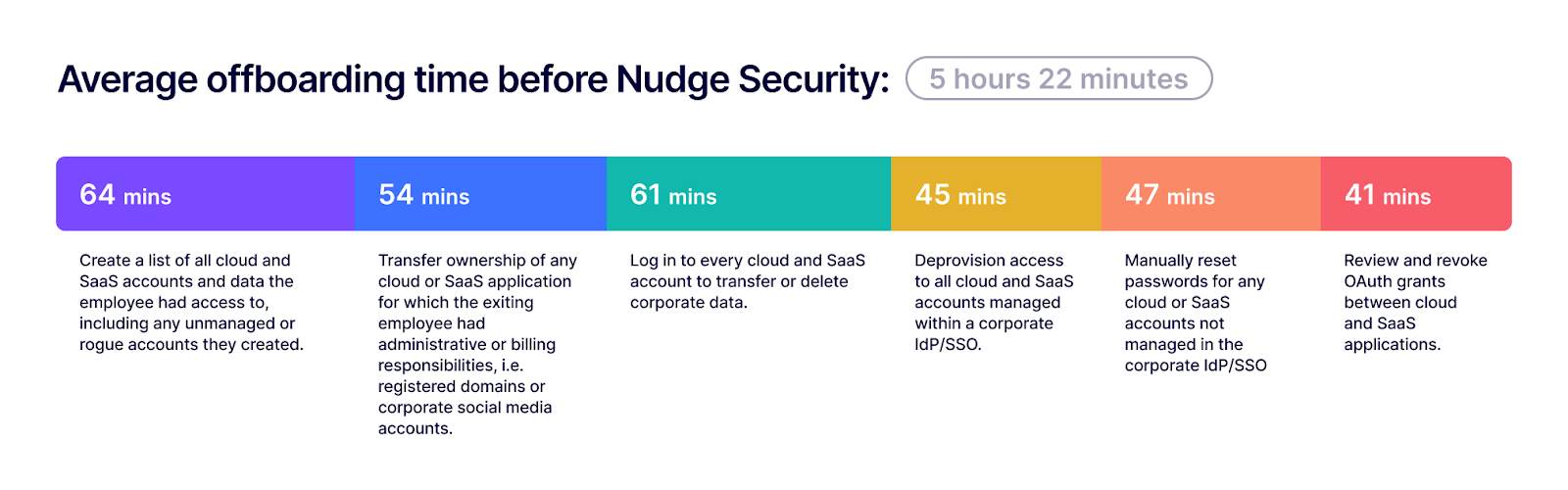
It’s worth mentioning that this list of activities is specific and non-exhaustive. Organizations may perform additional tasks to deprovision access to IT systems. The list does not account for time spent on other offboarding activities, such as deprovisioning devices and conducting exit interviews. The overall time investment of employee offboarding is likely much higher than the scope of this survey.
We asked, “What sources of information do you use to identify all cloud and SaaS accounts and data the employee had access to?”
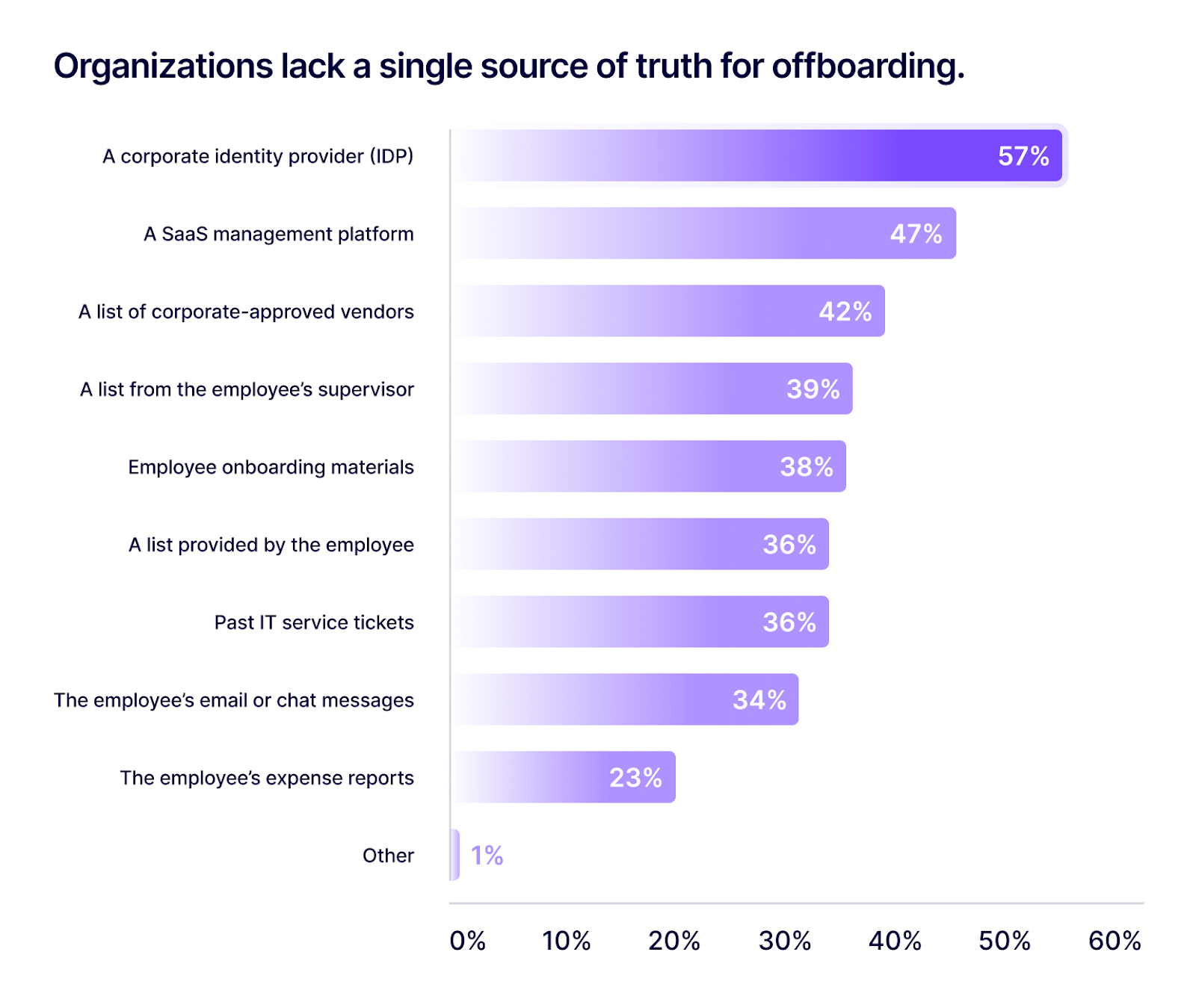
Given this finding, it’s no wonder IT organizations spend over an hour just to create a punch list of an employee’s cloud and SaaS footprint. This information is often fragmented across multiple systems and repositories, not to mention incomplete and outdated, leaving IT administrators to play the world’s worst scavenger hunt, cross-referencing multiple tools and lists just to get to the starting line of offboarding.
According to data collected from our platform, at a mid-sized organization (1,000 employees), a new SaaS account is created roughly every 20 minutes. Increasingly, SaaS accounts are created outside the purview of the IT organization, from remote and off-network locations, on personal devices, or as freemium subscriptions that don’t appear in corporate expense reports. As such, IT organizations struggle to maintain complete, consolidated visibility of their cloud and SaaS assets. This problem too often comes to a head during employee offboarding events, with IT administrators feeling the pain in the form of long Friday nights in the office.
To ensure complete employee offboarding, IT organizations need a single source of truth for all cloud and SaaS access—one that updates automatically as new applications are introduced and integrated with other corporate assets. Learn how Nudge Security performs SaaS asset discovery and inventory ->
It’s all too easy for things to get overlooked during employee offboarding. When it happens, the impacts to the business can vary, but often include:
We asked how often respondents had experienced the consequences of incomplete employee offboarding. 70% had experienced one or more of the following effects at least one time or more.
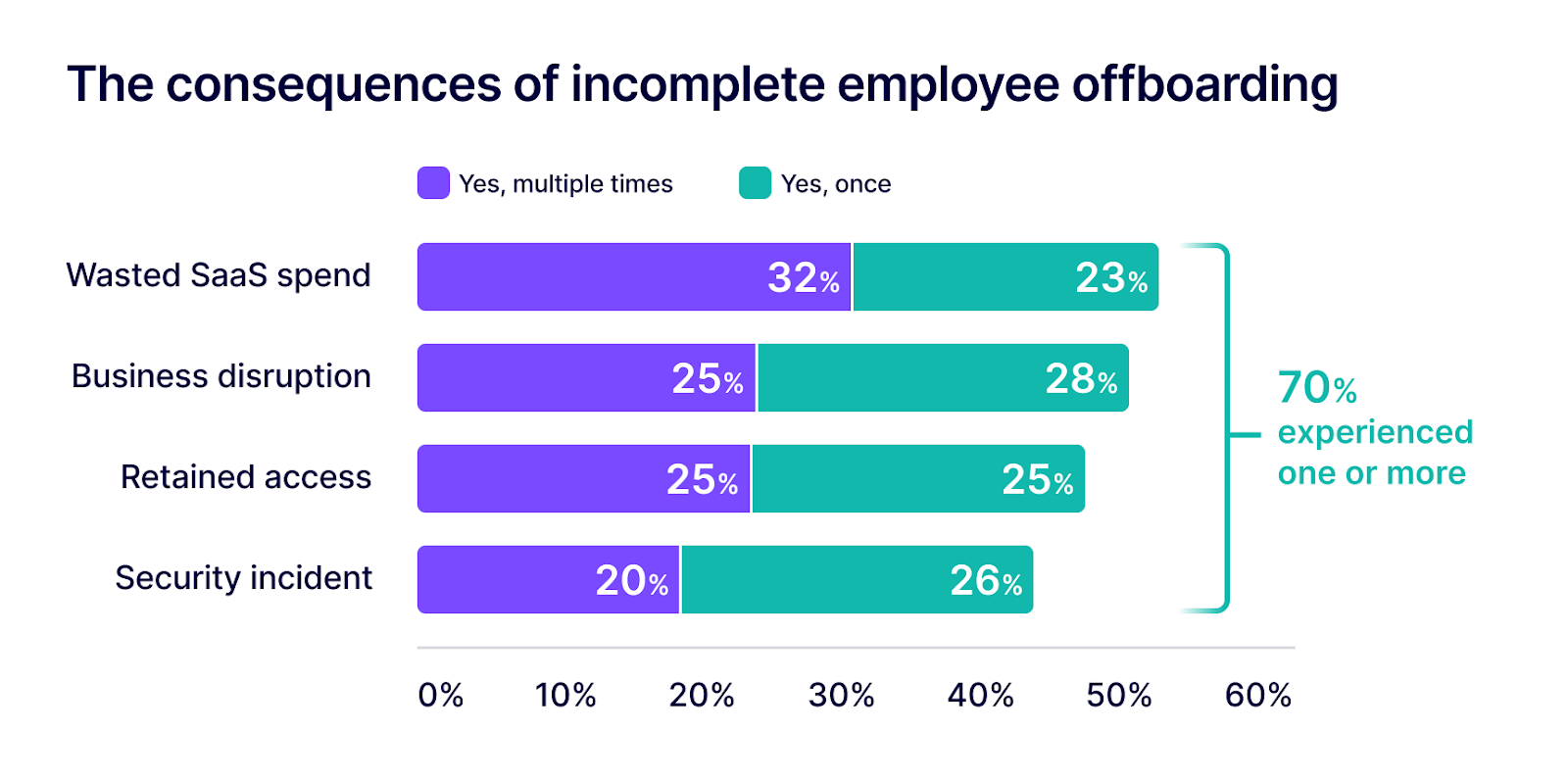
Note: See survey questions and response details for this section under “Additional data.”
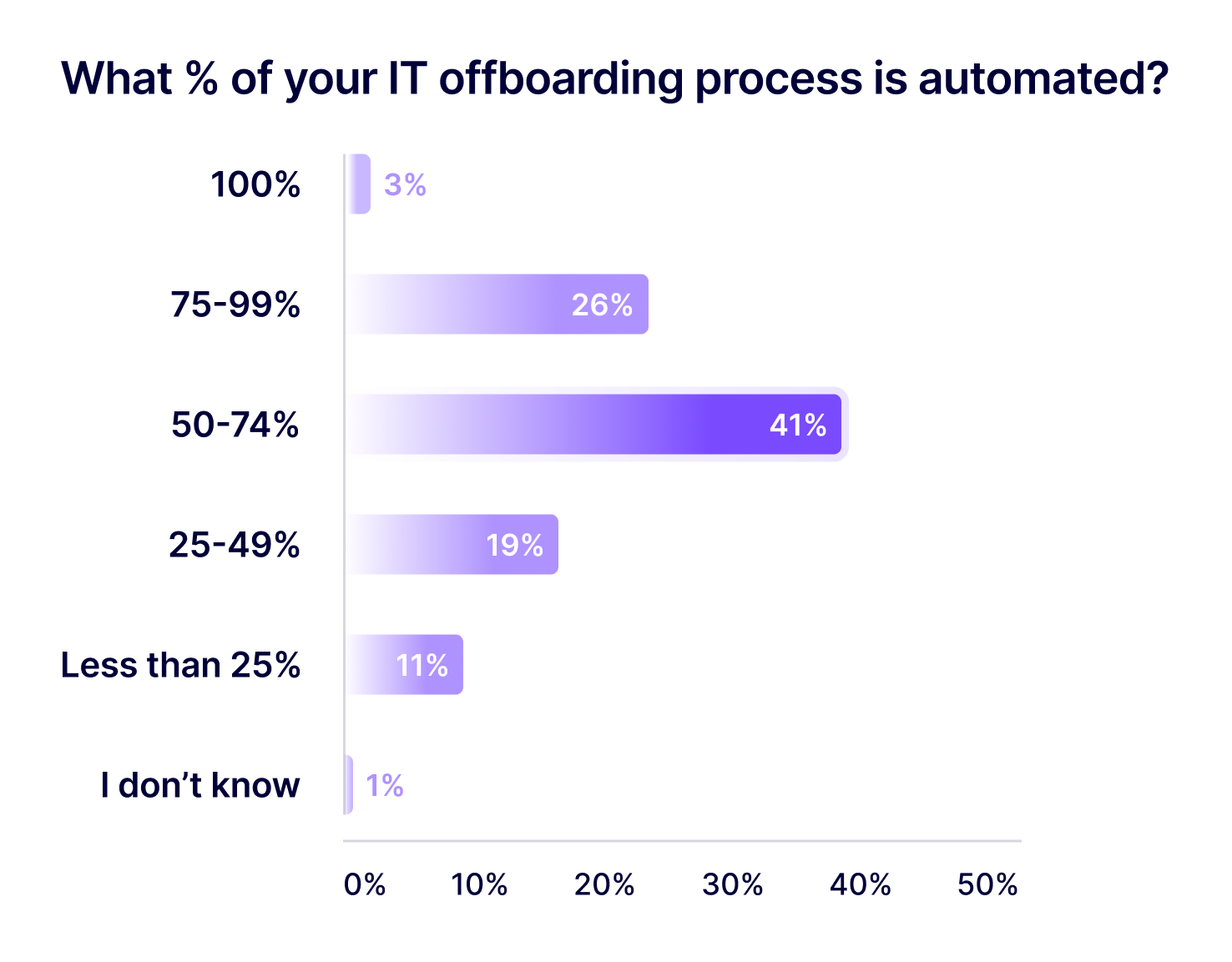
As it turns out, IT organizations aren’t hitting the easy button to offboard employees. Despite the prevalence of IdPs and SSOs used by respondents, less than one-third of them have automated 75% or more of their IT offboarding process. What’s more, higher rates of automation only slightly corresponded to reductions in time spent offboarding cloud and SaaS (~30 minutes), and only slightly corresponded to higher rates of confidence in being able to discover and deprovision all shadow IT. Only 58% of respondents who have automated 75% or more of their IT offboarding process were “extremely confident” in their ability to identify and deprovision all of the shadow IT, compared to 47% of respondents who have automated 50-74% and 45% of respondents who have automated 49% or less of their process.
The tedious parts of employee offboarding are considered difficult or impossible to automate—namely, finding and deprovisioning all shadow IT and coordinating with HR, departing employees, reporting managers, HR and non-IT business owners of SaaS applications. We specifically address these “impossible-to-automate” tasks in our new employee offboarding automation playbook.
We asked, “What percentage of your IT offboarding process is automated?”
Our new employee offboarding automation playbook targets the cloud and SaaS offboarding activities we included in our survey, turning 5 hours of manual IT effort per employee into an estimated 30 minutes or less, resulting in upwards of 90% time savings for IT organizations.
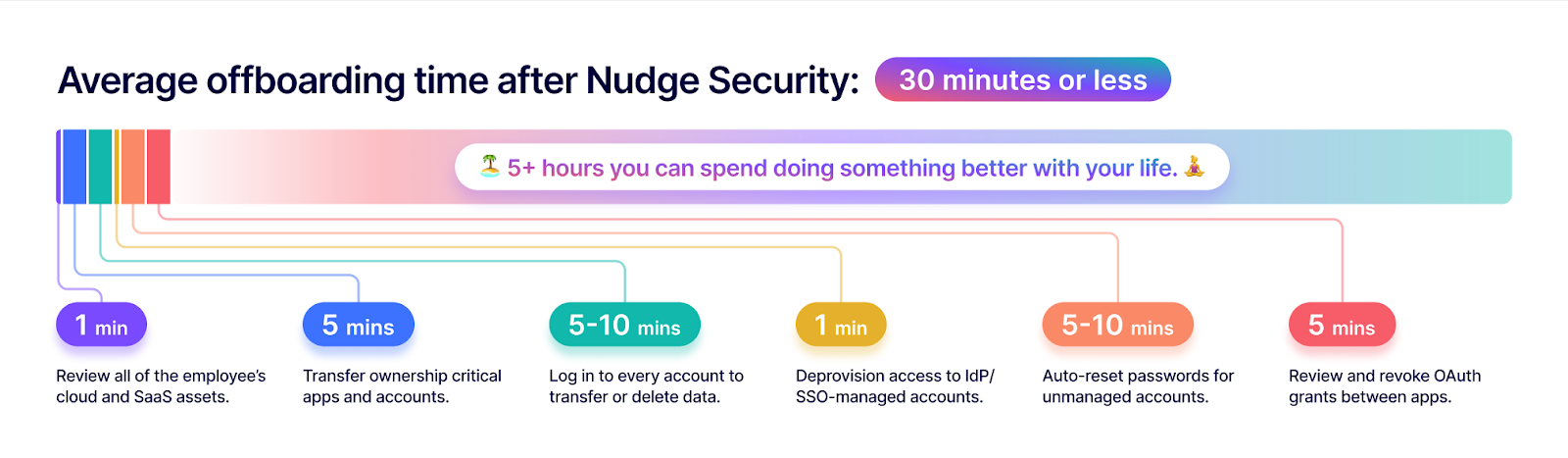
To learn more about our new employee offboarding automation playbook, read the tutorial on our blog. To try it out, start now with a zero commitment 14-day free trial of Nudge Security ->
Nudge Security conducted an online survey of 375 U.S.-based IT professionals who have some secondary education, are currently employed at organizations of 50 or more employees, and who participate in their organization’s employee offboarding process. Data was collected in April 2023 via an online survey conducted by a reputable third-party panel provider.
Involvement in IT offboarding
We asked, “When an employee leaves your organization, what is your involvement in the IT offboarding process? (n=377)
61% (n=230) of respondents said, “I directly perform some or all IT offboarding activities, such as deprovisioning accounts and wiping devices, for all employees. 23% (n=87) said, “I manage or oversee my organization's IT offboarding process.” 16% (n=60) said, “I directly perform some or all IT offboarding activities only for my direct reports or employees in my department.”
Job function
We asked, “What is your job function?” (n=377)
78% (n=295) of respondents reported working in IT, 12% (n=47) in Operations, 3% (n=12) in Engineering, 2% (n=9) in Security, 2% (n=7) in Compliance, and 2% (n=7) in Other.
Organizational role
We asked, “What is your job level?” (n=377)
42% (n=158) of respondents were middle management (director, departmental head); 24% (n=89) were C-level executives or board members; 18% (n=69) were senior management (VP, GM); 14% (n=53) were first-level management (manager, team lead, principal); 2% (n=7) had intermediate experience (senior staff, analyst); less than 1% (n=1) were entry-level employees.
Survey questions and results details: confidence in IT offboarding
We asked, “when an employee leaves your organization, how confident are you in your ability to identify and deprovision all of the "shadow IT" (unmanaged cloud and SaaS accounts and data) the employee had access to?” 49% (n=185) said they were extremely confident; 36% (n=135) said somewhat confident; 6% (n=21) said neither confident or unconfident; 5% (n=18) said somewhat confident; 4% (n=16) said extremely unconfident.
We asked, “Overall, how confident do you feel about the completeness and efficiency of your IT offboarding process?” 42% (n=149) said they were extremely confident; 37% (n=129) said somewhat confident; 7% (n=24) said neither confident or unconfident; 9% (n=31) said somewhat confident; 5% (n=19) said extremely unconfident.
Survey questions and results details: consequences of incomplete IT offboarding
We asked, “has your organization ever been affected by unnecessary costs related to incomplete IT offboarding? For example, you received a surprise bill for a former employee's account or money was wasted on unused SaaS licenses. 32% (n=120) said “yes, multiple times”; 23% (n=85) said “yes, one time”; 44% (n=162) said “no, not that I’m aware of”; 1% (n=3) said “I prefer not to say.”
We asked, “has your organization ever been affected by a business continuity issue related to incomplete IT offboarding? For example, you were unable to access a SaaS application after the admin left your organization or lapse in billing for a SaaS application or domain disrupted a business process.” 25% (n=94) said “yes, multiple times”; 28% (n=102) said “yes, one time”; 45% (n=168) said “no, not that I’m aware of”; 2% (n=6) said “I prefer not to say.”
We asked, “has your organization ever been affected by a security incident related to incomplete IT offboarding? For example, a former employee or threat actor gained unauthorized access to a cloud or SaaS application because the user credentials still worked.” 20% (n=73) said “yes, multiple times”; 26% (n=95) said “yes, one time”; 53% (n=196) said “no, not that I’m aware of”; 2% (n=6) said “I prefer not to say.”
We asked, “have you ever discovered that you personally still had access to a cloud or SaaS application of a former employer?” 25% (n=93) said “yes, multiple times”; 25% (n=92) said “yes, one time”; 48% (n=179) said “no, not that I’m aware of”; 2% (n=6) said “I prefer not to say.”